Social Engineering: How hackers Manipulate the Human Mind
Social Engineering: Most of us have encountered numerous cyberattacks based on different methodologies and form types. And one thing that we are witnessing is that these cyberattacks are becoming more…
Suspected Chinese hackers tampered with widely used customer chat program -researchers
By Raphael Satter and Christopher Bing WASHINGTON (Reuters) -Suspected Chinese hackers tampered with widely used software distributed by a small Canadian customer service company, another example of a “supply chain…
The Cyber Elephant in the Boardroom -Video Interview
What is hidden behind the Cyber Elephant in the Boardroom? I interviewed Mathieu Gorge, the CEO, and founder of VigiTrust, a cybersecurity company with clients in 120 countries. Mathieu has over…
EU proposes rules to sue drone makers
By Foo Yun Chee BRUSSELS (Reuters) – The European Commission on Wednesday proposed rules making it easier for individuals and companies to sue makers of drones, robots and other products…
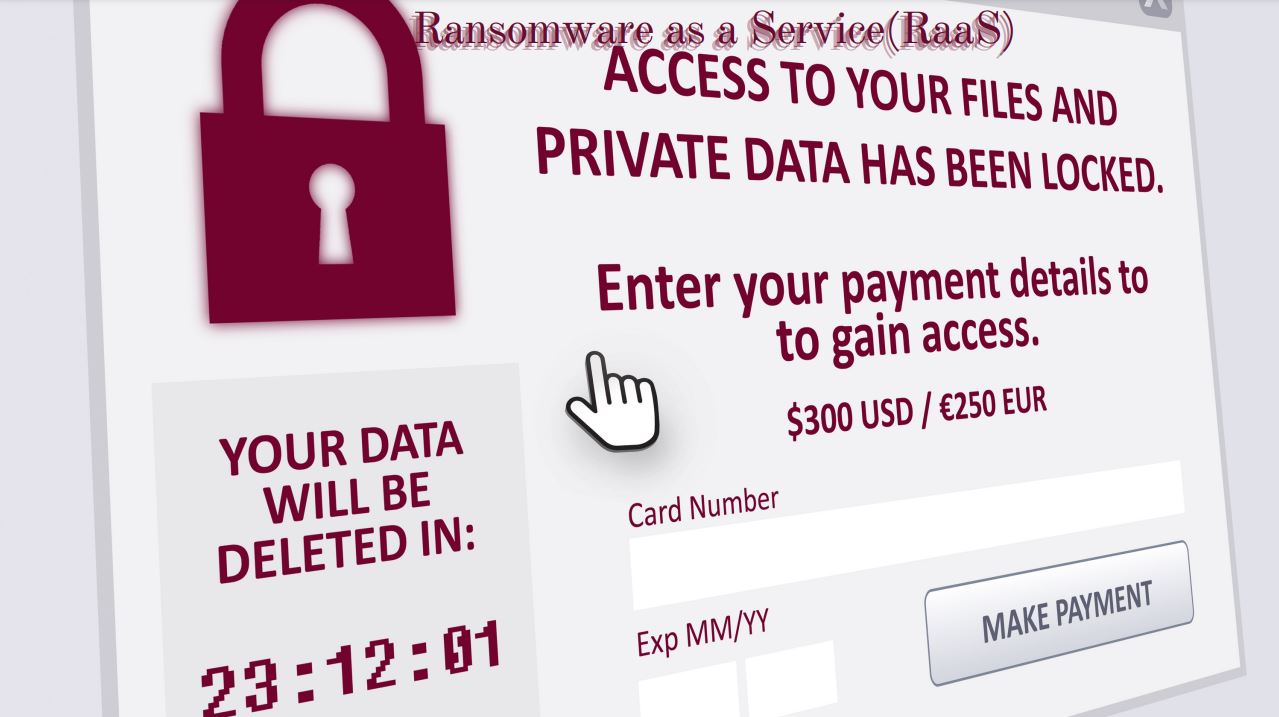
RaaS – Ransomware as a Service
RaaS: In recent years, the ransomware threat has continued to grow. The most apparent trend is that ransomware groups are now targeting larger businesses and, in doing so, can demand…
Exclusive-Brands blast Twitter for ads next to child pornography accounts
By Sheila Dang in New York and Katie Paul in Palo Alto; Additional reporting by Dawn (Reuters) – Some major advertisers including Dyson, Mazda, Forbes and PBS Kids have suspended…
Meet the talent: David Duke, ACI Learning
Place of residence: Chicago (the South Side), IL, USA Position: Chief Product Officer & Senior Vice President, ACI Learning ACI Learning Please describe a day in your life: I’m up…
Google to Build its First Cloud Region in Greece ATHENS
By Angeliki Koutantou ATHENS (Reuters) – Alphabet Inc’s Google will set up its first cloud region in Greece, the company said on Thursday, giving a boost to the country’s efforts…
Black Hat Hackers – Trying to Hack into their Mindset
Black hat hackers: Most people think that hackers are criminals. It is a common fact that most people don’t know that a broad category of hackers helps us differentiate them…
Albanian Cyberattack Continues
The infamous cyberattack that happened in Albania at the beginning of summer took every IT professional’s attention based on the attack’s nature. In July of this year, the Albanian government…