FACTBOX – Australia Inc roiled by raft of cyberattacks this year
By Jaskiran Singh FACTBOX (Reuters) – Australian firms have suffered a flood of cyberattacks, putting the spotlight on country’s understaffed cybersecurity industry which experts say seems ill-equipped to tackle such…
The Costs of poor API Protection and Common Pitfalls Discussion
During October, Cybersecurity Awareness month, 4i-Magazine hosted three live discussions related to cybersecurity topics. This discussion was associated with API Protection, and our speakers shared their knowledge regarding this topic.…
How to Intelligently Prioritize and Predict your Third-Party Risk
Third-Party Risk: During October, which was Cybersecurity Awareness Month, 4i-Magazine hosted three discussions related to cybersecurity. Our guest speaker was Courtney Cohen, Senior Director of Product, CyberGRX: Courtney is a former data…
TikTok denies that ByteDance used the app to monitor citizens
TikTok said it does not collect GPS location information from users in the US. A clarification that comes in the wake of a Forbes article, which instead pointed out that, according to…
November 2022 – Note from the Editor in Chief
November: I will say that Christmas Season is near. I know some people are really excited, and others do not want to think about this yet. But I am team…
Cyber officials from 37 countries, 13 companies to meet on ransomware in Washington
By Andrea Shalal WASHINGTON (Reuters) – The White House will host officials from 37 countries and 13 global companies in Washington this week to address the growing threat of ransomware…
Ransomware hackers hit Australian defence communications platform
By Renju Jose SYDNEY (Reuters) – Hackers have targeted a communications platform used by Australian military personnel and defence staff with a ransomware attack, authorities said on Monday, as the…
Cyber Halloween – Just take the treat, but do not get tricked
Cyber Halloween is just around the corner, and you can already sense the spookiness in the air. But this month is not all about Halloween, tricks, and treats; it is…
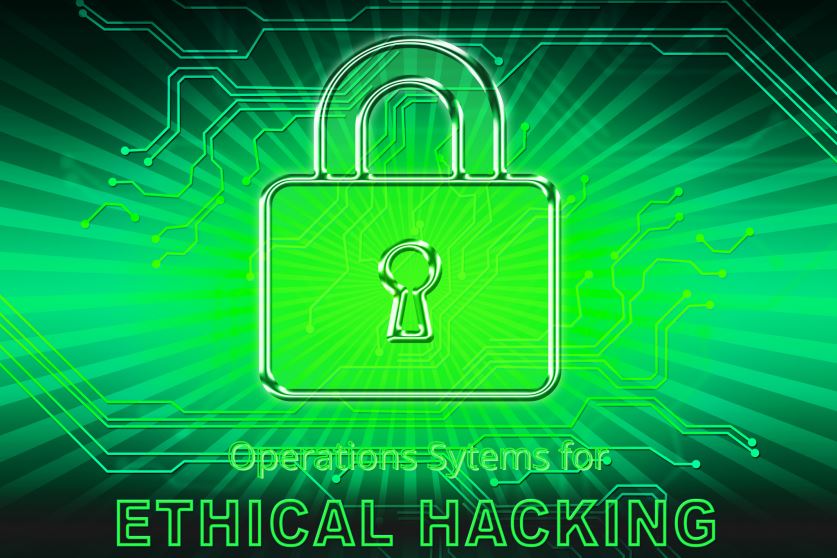
Operating Systems for Ethical Hacking
Ethical Hacking is intentionally breaching an information system’s security to detect vulnerabilities in it and then fix them. Ethical Hackers conduct tests with the consent of the organization whose server…
Halloween apps to get you into the Spooktacular spirit!
With Halloween just around the corner, we take a look at some of the spookiest apps for both the dead (and alive!) on the internet. The annual celebration had technology…