How can we take Data Privacy and Protection to the next level?
Today we can say that we have reached a new peak of advanced technology. At the same time, as technology grows more powerful, data protection security and privacy vulnerability increases along with the fast-paced developments in the tech world. The amount of data is increasing daily since more companies are becoming digitalized and data-driven. But with this increase, the risk from malicious attacks has never been higher. Cyber-attacks are becoming more sophisticated, driven by the intent of compromising different information systems by taking advantage of a vulnerability or weakness in a system or individuals of any company or organization.
Attackers aim to get unauthorized access to sensitive information or corrupt information systems and manipulate, delete, or destroy data. All these actions have a lot of consequences in the business world that result in great damages to the point where it could lead to business interruption or even bankruptcy.
GDPR
In these circumstances, hackers have become organized, share tools and access advanced technology like quantum computing. It’s important to tap into a combination of security approaches to ensure maximum protection. Until now, most organizations have followed the approach of dividing cybersecurity, data protection, and privacy into different categories, but in reality, these two concepts are very connected and depend on each one’s progress.
Cybersecurity focuses on specific technical methodologies used to protect information systems. We are talking about different techniques used to audit procedures, perform penetration testing to find vulnerabilities and gap holes, and develop specific methods and solutions to help secure the systems so they can become harder to penetrate. Meanwhile, when discussing data protection, we mention procedures to safeguard personal data stored within a system.
Data protection addresses data management, availability, unauthorized access prevention, and application regulations like Health Insurance Portability and Accountability Act (HIPAA) or General Data Protection Regulation (GDPR). Unlike cybersecurity, which is a set of technical actions performed by a specific cybersecurity specialist, data protection focuses more on procedures. It requires effort from all the people that are part of an organization since it is the duty of all to maintain safety data. But even though they seem very different, the combination of both can be done easily, and we can benefit significantly from it.
Combining cybersecurity and data protection
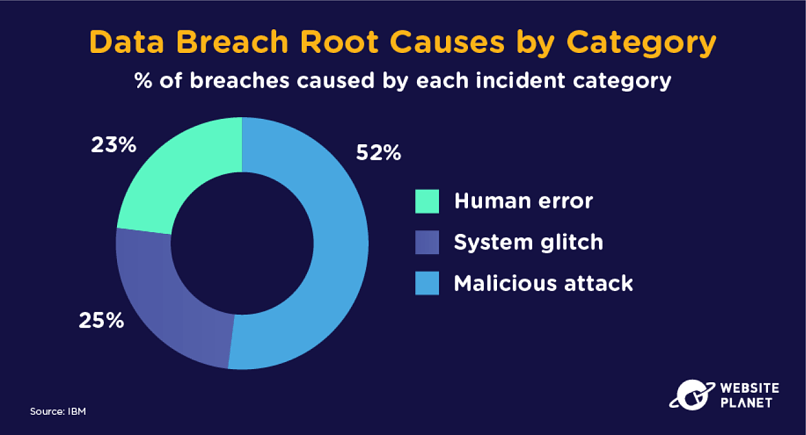
Data breaches are the perfect examples of how data protection and cybersecurity must be combined to achieve excellent safety in our systems. It is common knowledge that data breaches affect various aspects of an organization’s life cycle. And to prevent these data breaches, cybersecurity and data protection should combine since we’ll be overseeing both data and systems simultaneously, leaving less space for vulnerabilities and exploits. Also, we’ll be able to enhance the information security management system. A single ISMS platform allows you to control your data better than a separate infrastructure for data protection and cybersecurity. Another benefit from this combination is compliance improvement, which can be achieved by reducing the probability of data breaches through cybersecurity technical strategies—both data protection and cybersecurity deal with protecting sensitive data from various digital threats. Rather than having them respond to a breach separately, it makes sense to have one integrated approach.
Security Strategy
In order to face and prevent data breaches or any other cyber-attacks, organizations should adapt their everyday workflow and processes to data protection and the best defensive security strategies. One of the main things that should be done to combine the two is to gather all the skills necessary in one place or team. By investing in the skill sets of security specialists and professionals, we are creating groups that are able to see problems from different perspectives and come up with proactive and reactive solutions.
But the skills are not the only thing that can help join the two security units. Creating procedures and protocols to follow about data management and implementing them into the daily organization’s workflow is another way we can help in combining the two aspects. Ideally, we need an all-reaching plan that includes the design of the systems, maintenance, data management and access, and incident response.
And last but not least, one crucial part that helps in grouping and creating a safer environment is investing in awareness of the users and staff. Because anyone in an organization can cause a data breach, responsible user behavior should be an essential part of the corporate culture. For example, every employee must understand that a data breach can start from a routine action like installing software as a service (SaaS) app that may be fake.
A practical approach for enhancing more security in data protection
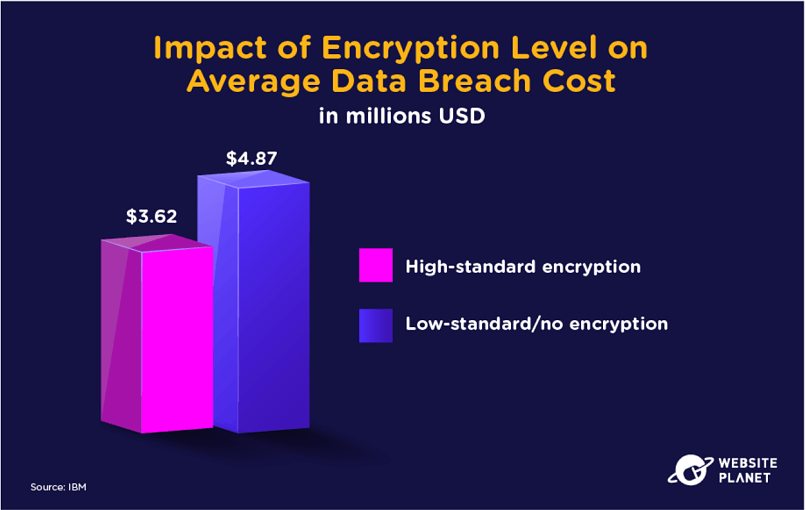
Until now, the traditional way of securing data has relied solely on data encryption and protecting the encrypted key. This method has proved very effective if implemented correctly, using random keys and not reusing the same one repeatedly. But this method is not hacker-proof because crucial management is still in the hand of users, and the risk of getting the key compromised from the normal user is very high. That is why it is needed a new approach to help in enhancing data protection strategies – the decentralized cybersecurity approach. Techniques from this approach split the data into multiple pieces, making it nearly impossible to reconstruct unless a quorum of splits is used. Since the full scope of data is not accessible, the attackers have no chance of accessing it, which makes the system quantum-proof and immune to all breaches.
So, we can understand that data privacy and protection strategies can be elevated by using different cybersecurity methodologies and techniques. An organized and combined approach can help devise the most optimal plan in facing the increasing threats of cyber attacks.



