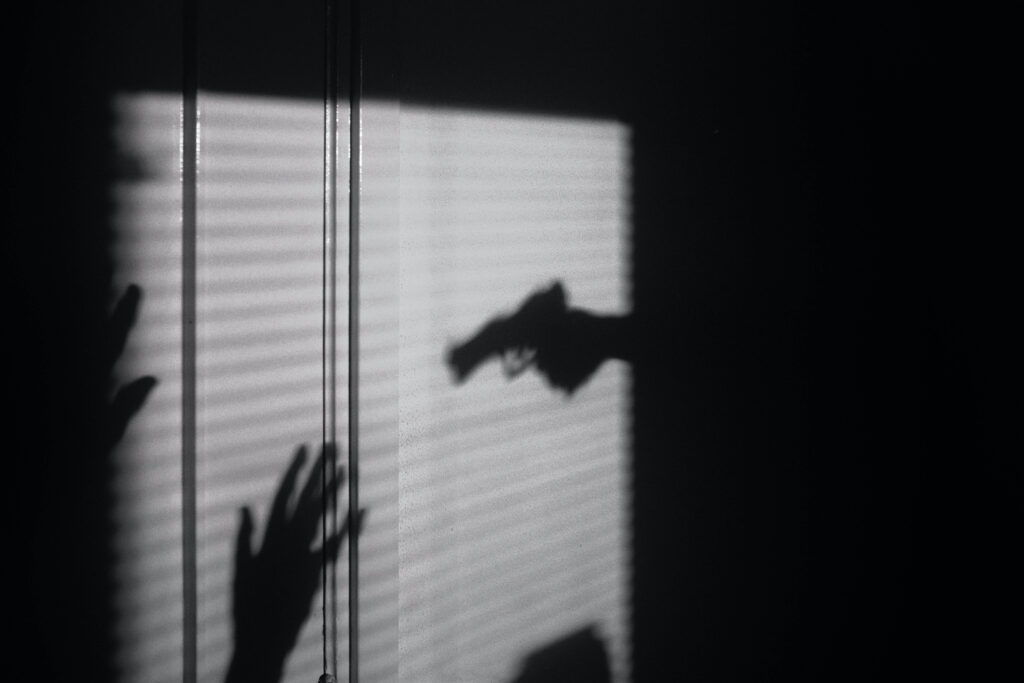
It has been said that the cybersecurity word of the year is ‘resilience’ — but it could just as easily be ‘ransomware’. A report from eSentire’s Threat Response Unit (TRU) indicates that cybercriminals, leveraging extortion through ransomware attacks, are broadening their targets and making millions of dollars in illicit earnings.
The report studied the activity of the four most prominent ransomware gangs in the world, along with that of two emerging contenders. Although not a new problem, the ransomware phenomenon has grown to dominate the threat landscape and is no longer the concern of institutions and government organisations alone.
Adaptation
Historically, targets for ransomware gangs have included state and local government, schools, law firms, and more recently, hospitals; notably, ransomware attacks on healthcare in Ireland, New Zealand, San Diego, and Düsseldorf have made headlines.
As well as fitting these patterns, the six gangs in focus have broadened their appetites, targeting manufacturers, transportation and logistics companies, and construction companies, in the United States, Canada, France, the United Kingdom, and parts of South America. One of the gangs was responsible for the Colonial pipeline attack that shut down energy supply for millions of citizens in the United States.
Based on the gangs’ own website posts and leaks, they have struck 292 companies between the period stretching January 1st to April 31st, 2021. Victims tend to keep the matter private, for fear of consequences to their reputation or business prospects. This means that no matter how prevalent ransomware appears to be in the media, the problem is far worse below the surface.
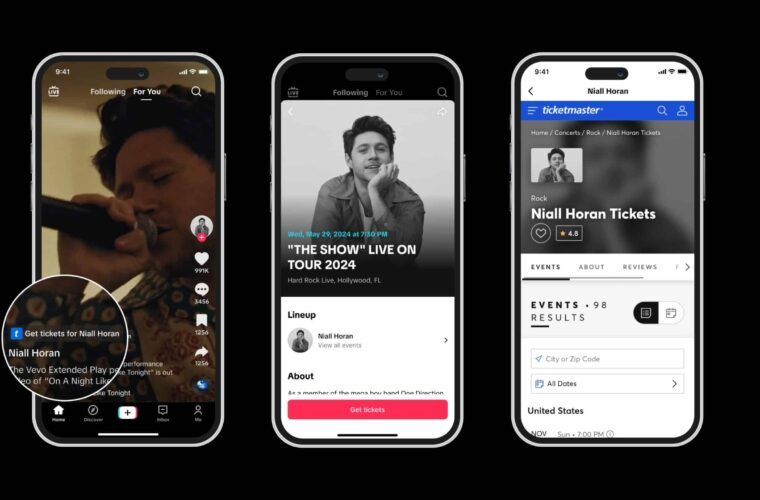
To get a sense of the scale of the issue, TRU teamed up with Dark Web researcher Mike Mayes, tracking the Ryuk/Conti, Sodin/REvil, CLOP, and DoppelPaymer ransomware groups, as well as emerging gangs DarkSide and Avaddon.
The report cites an estimate that the true global cost of ransomware, including business interruption and ransom payments in 2020, was between $42 billion and $170 billion. A separate survey by Veritas Technologies found that 66% of victims admitted to paying part or all of the ransom.
Palo Alto’s Unit 42 Ransomware Threat Report indicates that the average ransom organisations paid increased from $115,123 in 2019 to $312,493 in 2020, a 171% year-on-year increase.
The TRU report used the numbers for 2020 and conservatively assumed that only half of the alleged victims paid the ransoms. By this logic, the total earnings for just these six groups, in the past four months alone, could have been $45 million.
The cost of paying
Most organisations cannot afford to refuse payment: the unrecoverable encryption of their data would be catastrophic to their business. At the same time, many victims who pay out are hit again months later, particularly when confidential data leaks are a part of the equation.
This endemic issue is creating a vicious cycle. If companies pay, then hackers have an effective way of making money, and the problem only intensifies.
Security companies are calling for more use of their services – an understandable if self-serving prescription. There are also some experts who encourage companies to assume that they will be hit by ransomware and to have cryptocurrency accounts set up in anticipation of needing to pay their extorters. At least then, time will be saved in not needing to set these things up under pressure. With less disruption, the cost to the business could be reduced, if only marginally. This pragmatic though limited solution gives some sense of how acute and complicated the problem is.

Other experts and politicians support introducing legislation requiring companies to submit incident reports for cybersecurity attacks, something that is being discussed in the United States right now.
With a clearer picture of the problem, solutions can be better tracked and assessed on the merits of their effectiveness. Companies will be able to leverage insights from the industry’s collective experiences with cyberattacks. This could also be used to bring cybersecurity into the light for formal business risk evaluation, improving insurance companies’ abilities to create suitable cyber risk profiles for their clients.
Such policies could foster higher levels of individual company responsibility in the area of cybersecurity. If having a poor cybersecurity rating would be known by customers and partners, the incentives to put safeguards in place would be that much greater.
Whatever the solutions that emerge, society clearly needs to adapt quickly. The cost of ransomware, and cybercrime in general, is staggering. And while we find our feet, the criminals are hard at work.