Explainer – What risks do advanced AI models pose in the wrong hands?
By Alexandra Alper WASHINGTON (Reuters) – The Biden administration is poised to open up a new front in its effort to safeguard U.S. AI from China and Russia with preliminary…
Highlights from Black Hat Asia 2024
Black Hat Asia 2024: The digital landscape is a battleground where hackers and cybersecurity experts constantly engage in a high-stakes game of cat and mouse. One event stands out as…
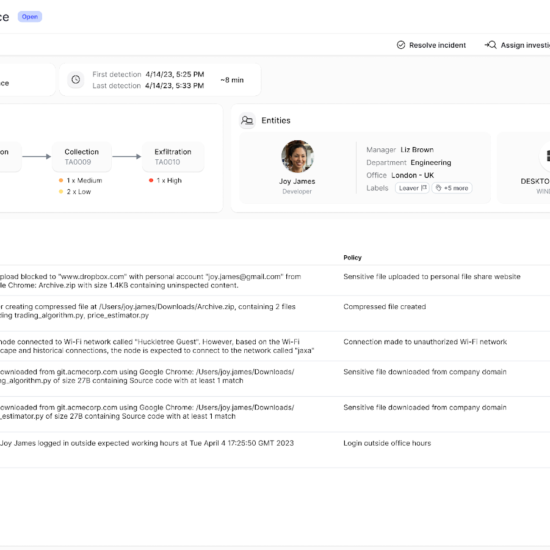
Next DLP announces first security solution to automatically map to MITRE’s insider threat knowledge base
Next DLP (“Next”), a leader in data loss prevention and insider threat solutions, announced that their Reveal Platform is the first Insider Risk Management solution to automatically map detection events to…
Enhancing IoT security: UK’s new regulations and HackerOne’s insights
The UK has implemented fresh security regulations for connected devices, courtesy of the Product Security and Telecommunications Infrastructure (PSTI) Act. This legislation lays down the foundation for security standards in IoT products,…
Copilot for Security: Microsoft announces the general availability
Copilot for Security: A growing area of interest in every company, cybersecurity is also at the top of the business functions that are most exploiting the power of AI by…
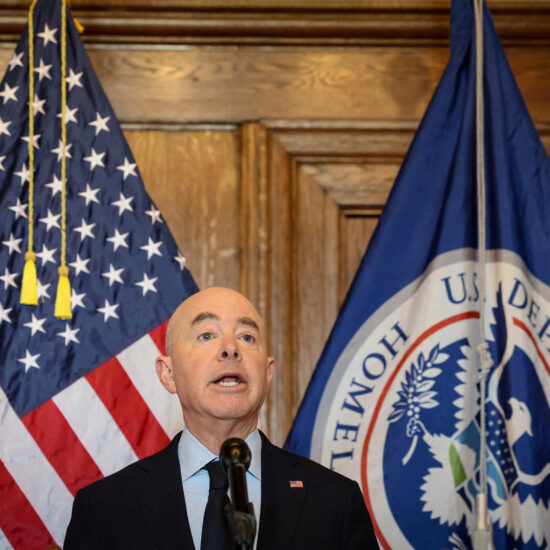
US Homeland Security names AI safety, security advisory board
By David Shepardson WASHINGTON (Reuters) – The U.S. Homeland Security Department (DHS) on Friday announced a blue-ribbon board that includes the CEOs of OpenAI, Microsoft, Google parent Alphabet and Nvidia…
Technology trends that will dominate 2024
Generative AI, semiconductors, quantum computing, batteries, and space technologies are some of the technology trends that will dominate in 2024—starting with generative AI, which between 2022 and 2023 conquered the…
Identity fabric immunity: what everyone needs to know
In today’s digital landscape, identity fabric immunity has emerged as a groundbreaking approach to cybersecurity, revolutionizing how we manage digital identities and mitigate cyber threats. Traditional identity and access management (IAM) systems struggle…
Fujitsu’s data breach: expert analysis from Chris Denbigh-White
Interview with Chris Denbigh-White: In a startling revelation, it has come to light that Fujitsu, a major player in the IT services industry, left crucial access keys and a LastPass vault…
What vulnerabilities are hidden from your cloud environment?
Cloud environment: The migration to cloud computing has revolutionized the way organizations operate, offering scalability, flexibility, and cost-efficiency. However, as we’ve ventured deeper into this digital transformation, the complexities and…