Cyber War: China and Taiwan
The United States House Speaker Nancy Pelosi’s trip to Taiwan made headlines in the region before and after the landing on 2 August. A few days before her trip, Chinese…
The New EU cybersecurity measures analyzed
The EU & Cybersecurity defined Cybersecurity is one of the Commission’s top priorities and a cornerstone of a digital and connected Europe. The rise in cyber attacks during the coronavirus…
Why Apple is moving manufacturing from China to India
Geopolitics, on the one hand, the zero Covid strategy as the only antidote to the spread of the virus on the other. These are the two main reasons that have…
Cyber officials from 37 countries, 13 companies to meet on ransomware in Washington
By Andrea Shalal WASHINGTON (Reuters) – The White House will host officials from 37 countries and 13 global companies in Washington this week to address the growing threat of ransomware…
With U.S. midterms ahead, Musk’s Twitter takeover raises fear of misinformation wave
By Joseph Ax (Reuters) -With the U.S. midterm elections less than two weeks away, Elon Musk’s $44 billion acquisition of Twitter could unleash a fresh wave of election misinformation just…
Career opportunity: The importance of cybersecurity
Career opportunity: Besides being a dominant theme due to the need to protect data from cybercriminal attacks, cybersecurity is today one of the best answers for young people looking for…
Cryptojacking and Cryptocurrencies
Cryptocurrencies’ creation and evolution have brought developments, new data, and challenges to the world of cyber security. A new type of cyber-attack has emerged, known as “cryptojacking.” Understanding and explaining…
Social Media and CyberSecurity in a Modern Era
Today, more than ever, our lives are online. We rely entirely on technology, such as our mobile phones and laptops, for our daily needs. When you fly through an airport,…
Cuckoo Sandbox – An interesting tool for malware analysis
Cuckoo Sandbox: Created by Claudio Guarnieri during the 2001 Summer of Code, the community has embraced it as one of the best digital forensics tools. In large part, this is…
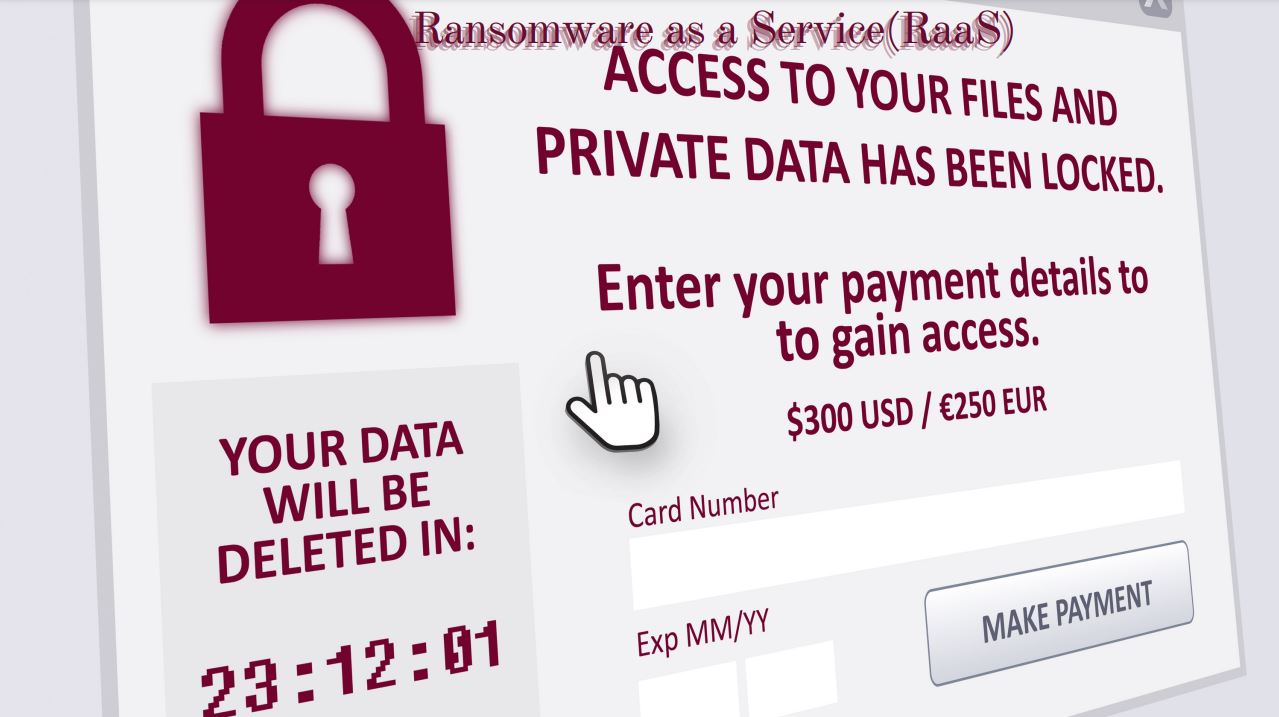
RaaS – Ransomware as a Service
RaaS: In recent years, the ransomware threat has continued to grow. The most apparent trend is that ransomware groups are now targeting larger businesses and, in doing so, can demand…