North Korean Hackers Send Job Offers to Steal Cryptocurrencies
A January report from Proofpoint, a security company based in the United States, says hackers affiliated with North Korea have been using an array of cyberattack methods, including phishing emails, to steal…
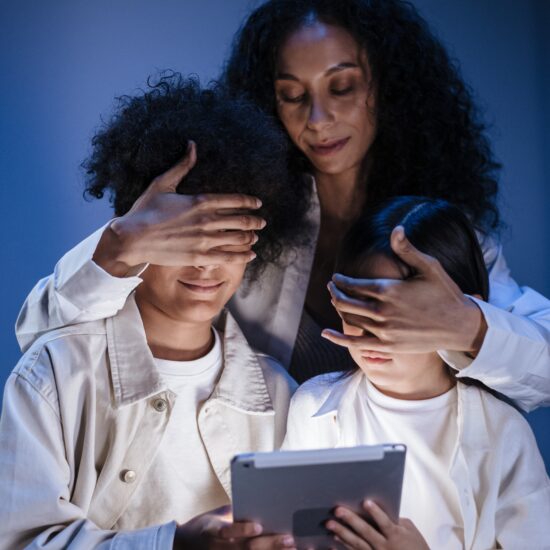
What is content filtering? Why have filter lists become a threat?
Ever wonder how different organizations, companies, or even parents manage to control what the regular user or child can see on their devices and limit different websites? Well, all of…
Record year for hackers, with North Koreans on top in 2022
Golden year for hackers thanks to crypto. Especially for the North Koreans, 2022 was their record year, as they made the highest amount of money. The alarm comes from a confidential UN…
ChatGPT Revolution: Will it impact the security world?
We are sure that by now, you have encountered or even tried the infamous ChatGPT, a very helpful AI-based application. The success of ChatGPT proves the effect of generative AI on…
Facebook investors urge revival of Cambridge Analytica fraud case
By Jody Godoy (Reuters) – Meta Platforms Inc investors formally asked a U.S. appeals court to revive a proposed class action accusing the Facebook parent of concealing a serious privacy…
The rise of cyber attacks during the holiday season: What you need to know
The holiday season is a time of joy, celebration, and gift-giving, but it is also a time of increased risk for cyber attacks. With millions of people shopping online, using the…
Britain’s JD Sports says customer data accessed by cyber attack
By Aby Jose Koilparambil (Reuters) – British sports and fashion retailer JD Sports Fashion has been the victim of a cyber attack which saw customer data relating to historical online…
A look back at the Top Security Issues of 2022: What we learned and how to avoid them in the future
2022 was a year of unprecedented events, and the security landscape was no exception. As the world grappled with the effects of the global pandemic on businesses and individuals, cybercriminals…
How to check if your internet browser is safe: The best tools you can use
It’s important to stay safe online, and one of the best ways to do this is by ensuring your internet browser is secure. It’s not just about keeping yourself safe,…
Hackers using OAuth malware to hijack email servers
OAuth has two main purposes on the web right now. Often, it is used to create an account and log in to an online service. OAuth 2.0 is an authorization…