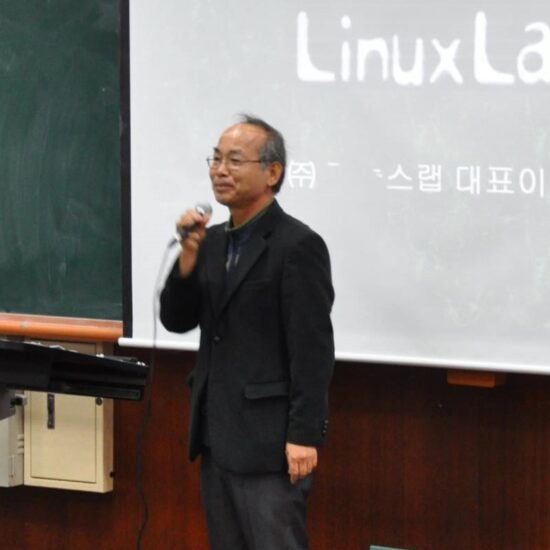
Meet the founder of one of the first VPN providers in South Korea
VPN providers in South Korea: Bae Cheol-su was a huge fan of the operating system Linux, released in the 1990s. Although he did not come from a background related to computer…
Nord Security: browsing made secure
Interview: Cho Sung-woo, Country Manager at Nord Security Soaring through its global competitors, NordVPN has become one of the biggest virtual private network providers across the world. NordVPN operates over…
Malware file scanners: how trustworthy are they?
Navigating the digital world demands vigilance, especially against different cyber threats, for example, malware. At times like this come malware file scanners, designed to detect and neutralize these cyber dangers,…
Canada bans WeChat, Kaspersky applications on government devices
By Ismail Shakil OTTAWA (Reuters) – Canada on Monday banned Chinese messaging application WeChat and Russian antivirus program Kaspersky on government-issued mobile devices due to privacy and security risks, but…
Ransomware’s infiltration of cryptocurrencies
Cryptocurrencies: Cyber attacks, once mere theoretical possibilities, have now become a grave threat to modern society. While ransomware attacks have become commonplace, some recent high-profile incidents have thrust them into…
Are Apple devices really immune to malware? (Spoiler: no, but almost yes)
The iPhone is the object that changed the perception of consumer technology. Before its appearance, hi-tech products were mainly confined to nerds and industry enthusiasts, who could only touch a…
What is malware? How to recognize, remove and protect yourself
Today, more than ever, we hear about malware. But what is it? The term refers to any software designed with malicious intent, usually an executable file that aims to damage,…
Top 30 cybersecurity tips and best practices in 2023
Top 30 cybersecurity tips: In an age where our lives are increasingly intertwined with the digital realm, safeguarding our information and privacy has never been more critical. The ever-evolving landscape…
IoC in computing: role and functions of indicators of compromise
When a cybercriminal attacks your company, he leaves a digital footprint. For example, your security team could detect cybercriminal activity in the system and record files after a cyber attack.…
Cybersecurity for dummies: what it is and why you SHOULD care
Cybersecurity for dummies: As digitalisation takes over the world, effective cybersecurity systems are more important than ever to organisations. You may have heard the term cybersecurity being thrashed about, but…