UK to work ‘constructively’ with Meta over encryption and online safety
By Sarah Young LONDON (Reuters) – British interior minister Suella Braverman said she wanted to work constructively with Facebook-owner Meta over the issue of end-to-end encryption on Instagram and Facebook…
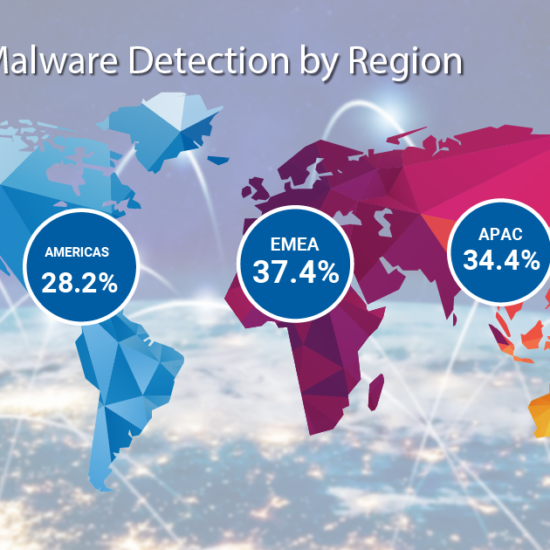
Unmasking invisible threats: Diving into the rise of encryption and fileless malware
Cybersecurity has taken centre stage in protecting us from digital harm in today’s hyper-connected world. This article invites you to explore encryption and fileless malware – two sinister foes that…
WhatsApp and other messaging apps oppose UK’s move on encryption
By Paul Sandle LONDON (Reuters) – WhatsApp and other messaging services have united to oppose Britain’s plan to force tech companies to break end-to-end encryption in private messages in its…
Google introduces end-to-end encryption on Gmail
Google brings end-to-end encryption to Gmail. In order to strengthen the confidentiality of the information that is exchanged every day via email, Big G has announced a beta dedicated to…
End to End Encryption (E2E or E2EE)
What is cryptography? Cryptography is the study of techniques based on mathematical problems difficult to solve, in order to ensure the security (confidentiality, integrity, authenticity) of data. Cryptanalysis is the…
Samsung Sets New Benchmark in TV Security With FIPS 140-3 Certification
Samsung Electronics announced that its proprietary cryptography module, Samsung CryptoCore,1 has earned the prestigious FIPS 140-3 certification2 from the National Institute of Standards and Technology (NIST). This certification underscores Samsung’s commitment to providing…
How to use ChatGPT to learn cybersecurity skills
As cybersecurity continues to evolve, professionals and learners are seeking new, efficient ways to acquire essential skills. One surprising yet effective tool for learning cybersecurity is ChatGPT, an AI model…
Cybersecurity in 2024: a terrifying reality
As Halloween approaches, the world of cybersecurity has never been scarier. The numbers speak for themselves: a 60% rise in phishing attacks, 43% of ransomware victims losing data permanently, and…
Samsung’s AI-powered home appliances are becoming more secure with Knox Matrix
Samsung Electronics is taking protection to the next level with Samsung Knox, the proprietary security platform safeguarding its AI home appliances, alongside additional solutions. The company aims to strengthen the…
World Space Week: space’s role in revolutionizing cybersecurity
As we celebrate World Space Week, it’s important to recognise how space exploration and technology continue to profoundly impact our lives. Beyond its contributions to global communication and navigation, space…